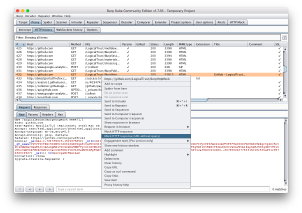
Burp HTTP Mock
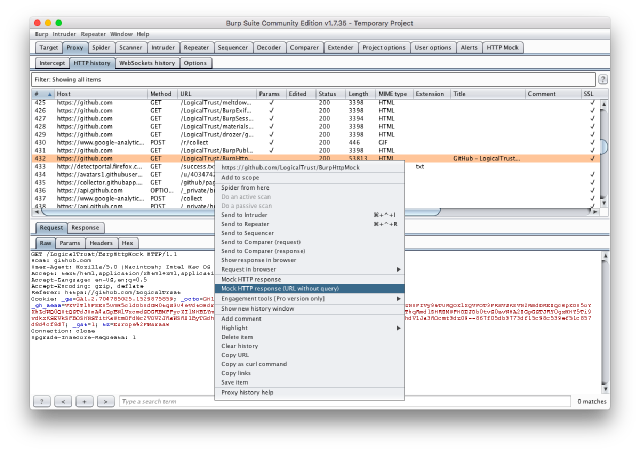
While on an assessment for a client I needed a way to intercept certain HTTP API calls and dynamically generate a response while allowing other calls to go through to the real application’s servers. I came across an extension for BurpSuite that allowed the user to select specific API calls to intercept and reply with static content, but I needed the ability to dynamically generate responses, so I added that functionality to the extension and published my changes. The extension now supports redirecting any HTTP request to any other URL, or replying to the call based on the contents of a file, or generating a response either by piping the content of the call to a program or by calling the program as a CGI script.
I spoke about and demo’d this extension at ToorCon 21. You can find my slides here.
You can find the original repository for the extension here and my updated fork on my work Github.
IoT Village SAO

As a fan of DEF CON’s #badgelife, I was ecstatic to have the opportunity to contribute as part of my employment at ISE. ISE runs the IoT Village at DEF CON and at other conferences, and we wanted to have our own badge… an effort which I unfortunately couldn’t see to completion while I was there.
In the meantime, I worked with the marketing team at ISE to create this, the IoT Village official SAO. It features artwork by ISE’s talented ‘social media guy’ cum salesman Sam Levin. I worked with him to import the artwork into KiCAD, designed the rest of the PCB (it makes an LED glow, very complicated 😉), and oversaw the manufacturing process including cost optimizing the BOM and working with our PCB fabrication house to ensure the quality was up to spec.
The SAO debuted in 2018 and has seen several ‘reprints’, so keep an eye out for one if you’re at a conference with the Village.
Misc. Burp Tooling
Much of my job consists of working with BurpSuite, so I find myself regularly needing to write small custom tools for working with it. I publish the ones that I can in the hopes that someone else might find them useful. Here are the ones I’ve published so far:
- Burp Extension Maven Archetype — After writing a couple extensions I got tired of manually instantiating the project structure, so I wrote a Maven archetype that does it for me. One command gets you a project directory with the right imports and a copy of the PortSwigger “Hello World” demo extension’s code ready to modify into whatever you need.
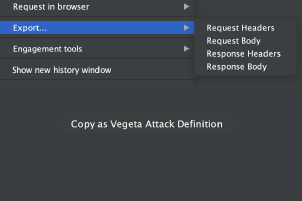
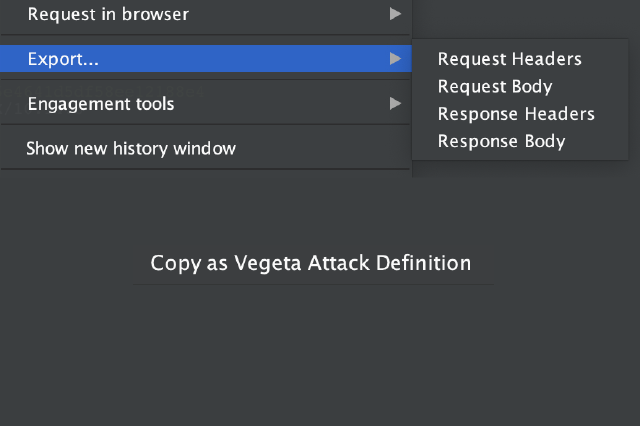
- Burp Easy Request Saver — Burp doesn’t have a fast way to export the binary contents of requests or responses, so I wrote one. It adds context menu entries to any request that lets you export the request or response headers or body to a file keeping all binary data intact. If you select multiple requests, each gets its own file.
- Burp2Vegeta — I was asked by a client to perform load testing on their service to simulate a Denial-of-Service attack. I decided to use Vegeta to perform a classic request flooding attack, but I needed a way to quickly tell it how to send correctly-formatted API requests. As a result I wrote a small Burp extension that exports any request(s) as Vegeta JSON attack definitions to the system clipboard. You can then paste them into an attack definition file and fire away.